By: John Halfacre – 22Jan2017
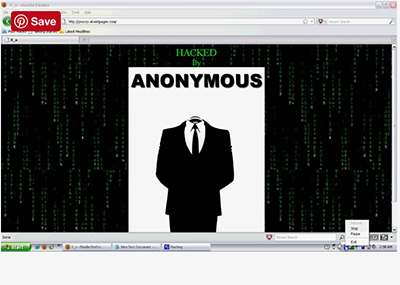
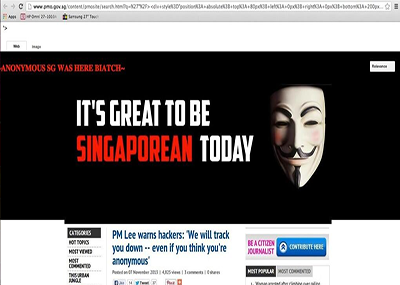
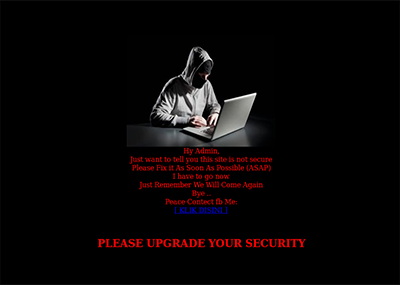
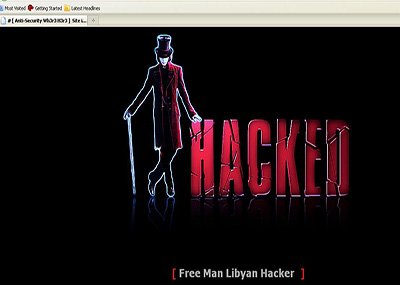
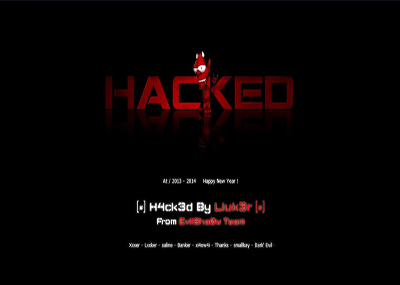
Website defacement refers to unauthorized changes made to the appearance of a webpage or website. In some cases, an entire website may be replaced by unauthorized content, while in others, a third party may inject code that adds irrelevant or inappropriate images, pop-ups, or text that were previously nonexistent. Other forms of website defacement include inserting malicious code which may infect visitors’ computers with viruses. Hackers may commit website defacement for pure enjoyment, or in protest, as seen in the 2015 defacing of the Lenovo website, in protest against the Superfish controversy by a group of “hacktivists” called the Lizard Squad.